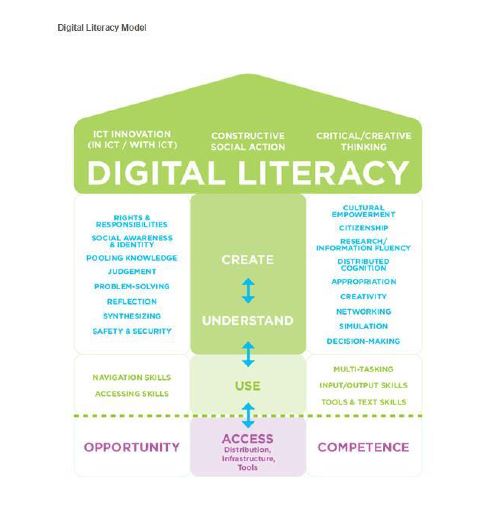
The great folks at Tech Soup Canada host a monthly series of talks, Tech Tuesday, and they recently invited me to share what I know about “Digital Literacy”. Little did I realize what I’d actually taken on. Digital Literacy isn’t just one tidy little topic. It’s actually a bunch of concepts, interwoven and far-reaching. Confused? You should be. I was. Which instantly galvanized me to distill a meaningful definition without diluting the impact of all the contributing factors as shown below:
Because Digital Literacy really means multiple literacies. So what we should fully appreciate is that it goes far beyond simply being able to use the technology, but also entails:
“The ability to locate, organize, understand, evaluate and analyze information using digital technology”. Wikepedia
I also very much liked this definition of what it wasn’t:
“Digital literacy is not simply a means by which we consume ever-increasing amounts of data and information, but a critical and creative means of interacting with the world.” Matt Dean
I’ll break it down to 3 core competencies:
USE: do we know how to use the range of technology available to us? And that’s a whole lot of devices
UNDERSTAND: can we comprehend the information, put it into context? More importantly, can we critically evaluate it? 2 words kept coming up when I did the research: Critical Thinking.
CREATE: Can we produce content, and then successfully communicate and share that content using the tools available? Content isn’t just words on a page. It’s graphic, visually impactive. It’s audio. It’s sensory.
Another big question raised repeatedly: What can you contribute to the online conversations that is unique? Websites, memes, infographics, blogs, videos and anything beyond that.

It’s all well and good to be familiar with the tech available and know how to use it. But baby, baby it’s a wide world out there and not everyone has the same techno advantages. Yes, I’m talking disparity aka known as “The Digital Divide.” One of the caveats I learned when researching Digital Literacy is that freedom of expression comes with digital constraints.
Being digitally literate requires that we understand our responsibility for accurately and safely curating and disseminating information. Think on that for a moment. Then think about our kids, in schools everywhere, and how they are actively engaging in online media as part of their curriculum. It would be nice to think there is a level playing field out there, especially when it comes to our kids in the classroom, but that’s far from the reality. According to CBC Tech columnist Jesse Hirsch, it’s “a pressing social issue.”
“The digital divide is a problem that goes beyond schools that needs to be closed not just with social policies but with the technology industry making sure their products are affordable.”
And this matters vis a vis Digital Literacy because it’s how we learn; how we engage; and how we work.
“Individual freedom and creativity, and societal and economic development, are becoming dependent on a degree of digital literacy.”
But regardless of what devices we use, the key to digital literacy keeps coming back to this: Critical Thinking. Just as we critically evaluate print media, we must also critically evaluate digital media. “Don’t believe everything you read” fully applies, especially when it comes to social media. Advertising has morphed along with marketing to target your preferences, and to trace your digital footsteps. It’s all about what we don’t know so I have put together a checklist of things we need to stay safe in our digital communities.
- Look for discrepancies, bad grammar, spelling errors. These are tip-offs that somebody is looking for something you don’t want to give them. Like access or personal information
- Don’t follow blindly. Not everyone is your friend, even on Facebook
- Wait! Don’t click that link. You’ve heard of breaches a lot over this past year. Well, phishing is how many victims get lured in. Malicious code is hidden in that cute attachment of kittens. Or in that website link you were sent. Evaluate!
- Malvertising. This is another way the bad guys go looking for easy targets. Many of those online ads actually contain malicious code that can redirect you to a website you never wanted to visit. And the worst is, it will follow you home and help itself to your information.
- Sponsored Ads. Technically, if someone is paid to promote something online, that’s sponsored and it needs to be disclosed. But that isn’t happening. You’d be surprised how they get around it and I’ll talk about that in a moment.
- Privacy. You have a right to your privacy. And your information should be kept private. But the internet is Pandora’s box. Once it’s out there, it’s out there for good and you no longer have control over it. Be very selective about what you sign up for and what you choose to reveal. Select All isn’t always the right answer.
This matters for everyone, but in particular it matters to our kids. This generation is growing up with technology in the classroom, at home, at play. The onus is on us, as their parents, to understand what they can and will be exposed to. Which is no small feat especially regarding privacy issues. The collection of personal information online has become commonplace, and is still done without our knowledge or consent.
Read through privacy statements to see how this works. An example comes from Lucid Press, who make a free design and publication app to integrate with Google Classroom. They encourage educators to sign up for a free educational upgrade and accounts for all their students. According to the privacy statement for Lucid Press:

Now, we know these aren’t the cookies that you dunk in milk. But what about web beacons or pixel tracking technology? A web beacon is typically a transparent graphic image (usually 1 pixel x 1 pixel) that is placed on a site or in an email. The use of a web beacon allows the site to record the simple actions of the user opening the page that contains the beacon. Because web beacons are the same as any other content request included in the recipe for a web page, you cannot opt out or refuse them. However, where they are used in conjunction with cookies they can be rendered ineffective by either opting out of cookies or by changing the cookie settings in your browser. This is from the site “All About Cookies” a free resource to help marketers and consumers understand the issues surrounding the use of cookies.
If I’ve made you stop and think, then this blog has served a purpose. Hopefully, I’ve given you answers to some questions, and prompted some questions you will now try to find answers for. To help you in that quest, these are some online resources you can look into:
As always, really glad you stopped by and thanks for reading!


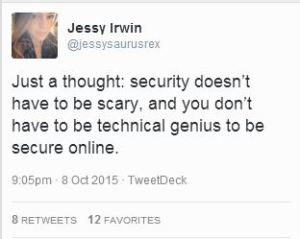



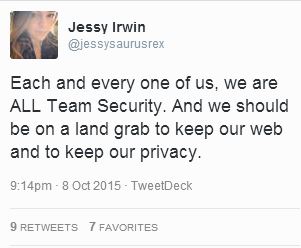




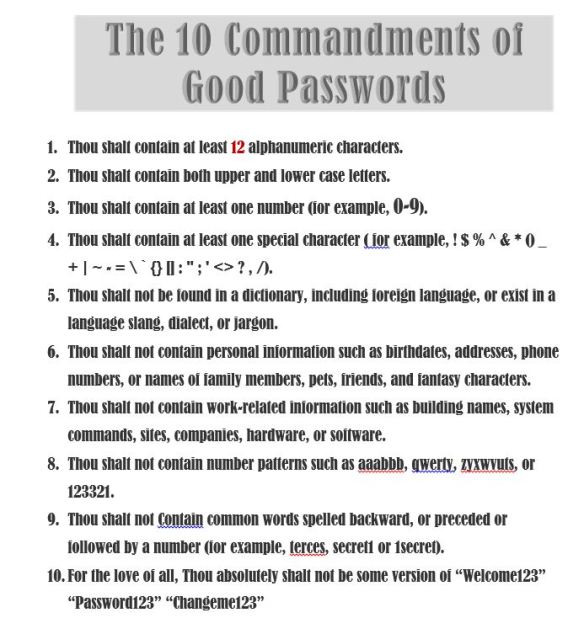
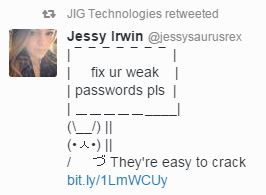 Bottom Line: Passwords are your first line of defence. Done right, they are an effective deterrent and the attackers move on. Done badly, you’ve just handed over the keys to your digital kingdom. I don’t have to remind you about the password file named “Passwords” from the Sony Hack. Or the sorry excuses for passwords (no – not actual excuses) emerging from the Ashley Madison dump. I highly recommend the helpful and direct guidance freely given by Jessy Irwin, the owner of the sign bunny to the right …
Bottom Line: Passwords are your first line of defence. Done right, they are an effective deterrent and the attackers move on. Done badly, you’ve just handed over the keys to your digital kingdom. I don’t have to remind you about the password file named “Passwords” from the Sony Hack. Or the sorry excuses for passwords (no – not actual excuses) emerging from the Ashley Madison dump. I highly recommend the helpful and direct guidance freely given by Jessy Irwin, the owner of the sign bunny to the right …




 (Image from
(Image from 




 Or better yet – how many zero days can you release in a week? Seriously, the time has come and the time is now to get rid of Adobe Flash Player. After Hacking Team got hacked a week ago Sunday, some of the spillage included several zero day vulnerabilities they had been sitting on. And while Flash seems to be a manufacturing plant of flaws that was no excuse. Hackers have been lying in wait for the good stuff to emerge. When it did, they were ready and jumped all over it. Exploits are booming. If we thought we had problems with folks clicking on stuff they shouldn’t before this, it’s going to be malware-palooza if Flash remains enabled. Mozilla was first to take direct response, and Firefox has blacklisted Flash Player. Who’s next?
Or better yet – how many zero days can you release in a week? Seriously, the time has come and the time is now to get rid of Adobe Flash Player. After Hacking Team got hacked a week ago Sunday, some of the spillage included several zero day vulnerabilities they had been sitting on. And while Flash seems to be a manufacturing plant of flaws that was no excuse. Hackers have been lying in wait for the good stuff to emerge. When it did, they were ready and jumped all over it. Exploits are booming. If we thought we had problems with folks clicking on stuff they shouldn’t before this, it’s going to be malware-palooza if Flash remains enabled. Mozilla was first to take direct response, and Firefox has blacklisted Flash Player. Who’s next?


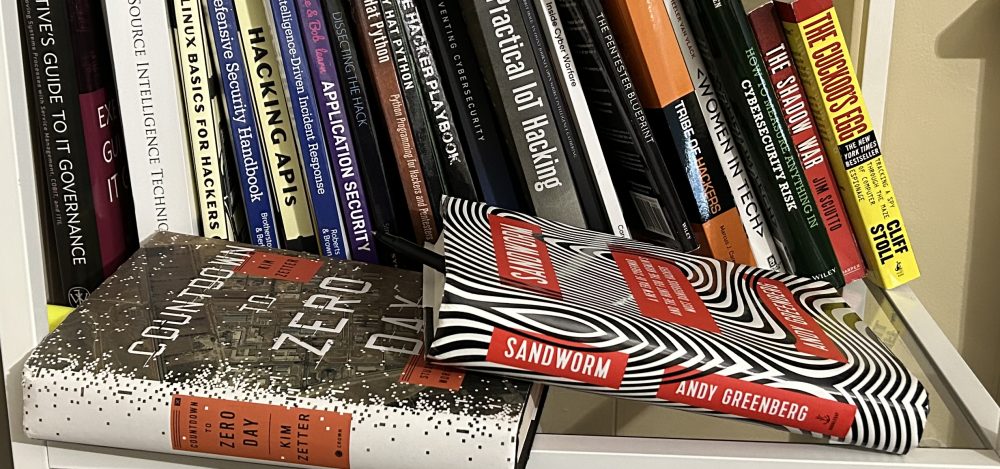
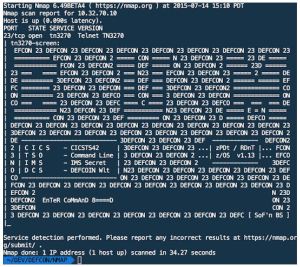
 Let’s clear up a big misconception. The hackers I know are definitely not this stereotype found ad nauseum. Yes, there are hackers who choose to attack our systems, steal data, and threaten our security. But there’s a whole other group out there who are also hackers, and in the constructive definition of the term. They “hack” to understand and improve the code and technology we use everyday; they test networks and programs, finding weaknesses and vulnerable points we need to defend from the attackers. Highly skilled and naturally curious, they understand our systems better than we understand ourselves. They know what can go wrong because they know how it can be broken, and that prevention is the best fix.
Let’s clear up a big misconception. The hackers I know are definitely not this stereotype found ad nauseum. Yes, there are hackers who choose to attack our systems, steal data, and threaten our security. But there’s a whole other group out there who are also hackers, and in the constructive definition of the term. They “hack” to understand and improve the code and technology we use everyday; they test networks and programs, finding weaknesses and vulnerable points we need to defend from the attackers. Highly skilled and naturally curious, they understand our systems better than we understand ourselves. They know what can go wrong because they know how it can be broken, and that prevention is the best fix. The best connections however, aren’t plugged into the network, but those made within the network of attendees. This is a community. There is an open camaraderie as folks who spend most of the year connecting online enjoy this opportunity to connect face to face. Attendees wear t-shirts from the past cons they’ve attended. Badges on lanyards denote speakers, participants, staff, and trainers. Tattoos are a walking montage of art and personal expression. Some describe themselves as introverts, but at these Cons they are among friends, accepted and welcomed. And then there are the parties, when hackers come out to play and the fun lasts all night long. A series of artful DJs delivered a wicked sound and light show as a wish-list of arcade games beckoned and we talked until we lost our voices. Yes, Alice, welcome to InfoSec!
The best connections however, aren’t plugged into the network, but those made within the network of attendees. This is a community. There is an open camaraderie as folks who spend most of the year connecting online enjoy this opportunity to connect face to face. Attendees wear t-shirts from the past cons they’ve attended. Badges on lanyards denote speakers, participants, staff, and trainers. Tattoos are a walking montage of art and personal expression. Some describe themselves as introverts, but at these Cons they are among friends, accepted and welcomed. And then there are the parties, when hackers come out to play and the fun lasts all night long. A series of artful DJs delivered a wicked sound and light show as a wish-list of arcade games beckoned and we talked until we lost our voices. Yes, Alice, welcome to InfoSec!