This October marked the 10th anniversary of Toronto’s main security conference, Sector. I had the pleasure and privilege of being a speak, as well as working with a terrific team of volunteers. It was thrilling to be part of this event, plugged right in, to welcome people to our city and then to deliver a talk I had really wanted to give.
There was fanfare. Edward Snowden – yes, for real- was video conferenced in as the keynote speaker Day 1 and he did not disappoint. He has put his time away to good use, becoming expert on matters of privacy and rights. There was a second terrific keynote panel on Day 2 by a group of very successful and talented women about their experiences and insights on careers in InfoSec. The selection of talks and speakers was truly impressive, featuring leading experts and exciting new voices.
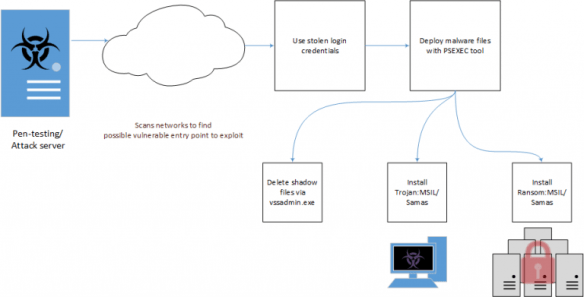
Here is my presentation, that started from a story on the Defensive Security podcast back in March. What caught my attention was how a bank heist in Bangladesh for a billion dollars was bungled because of a spelling error, and how far things almost went. Bank heists make great stories. This year, we’ve got some really good stories to tell courtesy of a trusted network known as SWIFT, and some banks that believed they were inherently protected by virtue of being connected – except they weren’t. Hundreds of millions of dollars have revealed some ugly truths and dangerous assumptions. In this security fairy tale we’ll talk about scary godmothers, big bad wolves, fire breathing dragons and what’s inherently wrong with the banking system. Because the emperors have no clothes on. Click on it to go to the site.